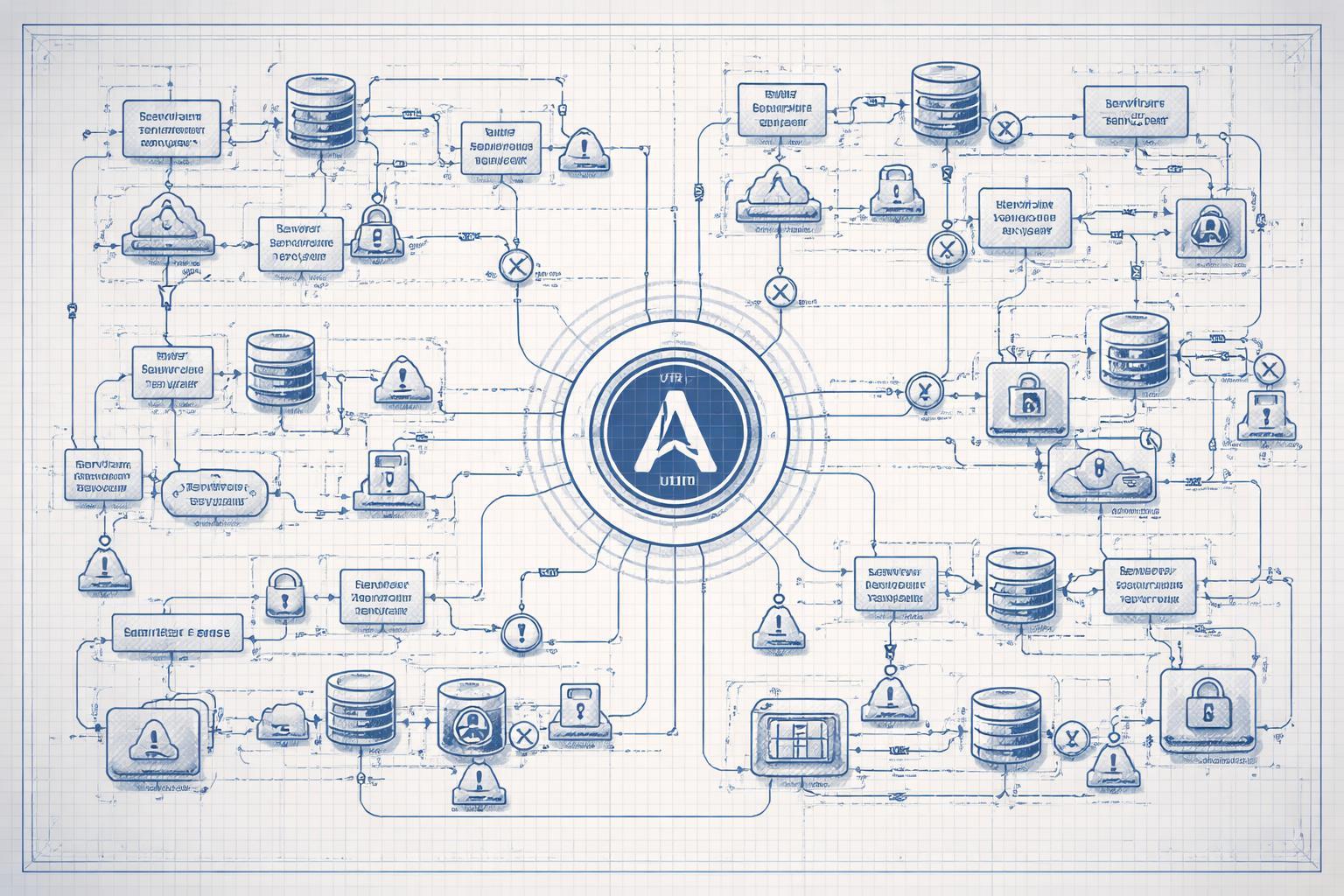
Attack Overview
Attackers have targeted government and public-sector organizations by exploiting OAuth 2.0's error handling mechanisms. The attack began with phishing emails containing malicious links. When victims clicked these links, they were redirected through legitimate OAuth authorization flows to malicious OAuth applications registered in Microsoft Entra ID. These applications used OAuth's error redirection behavior to bypass traditional phishing defenses and multi-factor authentication, ultimately delivering malware to victim systems.
The key takeaway: attackers didn't break OAuth—they understood its specification better than most security teams do.
Attack Sequence
The attack pattern follows a predictable sequence:
- Initial access: Phishing email delivered to the target organization.
- User action: Victim clicks the link, initiating an OAuth authorization request.
- Redirection exploitation: OAuth error flow redirects the user to an attacker-controlled endpoint.
- Consent abuse: User unknowingly grants permissions to a malicious OAuth application.
- Post-compromise: Malware delivery and potential lateral movement.
The speed of this attack is its strength. From click to compromise can happen in under 60 seconds—faster than most security teams can detect and respond.
Failed or Missing Controls
Application registration controls: Organizations allowed external OAuth applications to be registered and granted permissions without sufficient vetting. Your identity provider should treat application registration as a privileged operation requiring approval workflows.
Consent policies: Default or overly permissive consent policies allowed users to grant OAuth permissions to untrusted applications. This violates the principle of least privilege at the identity layer.
Phishing detection: Traditional URL filtering and email security tools failed because the OAuth flow involved legitimate Microsoft domains. Your security stack wasn't prepared for attacks that use legitimate infrastructure maliciously.
Error handling visibility: Security teams had no monitoring on OAuth error flows. When applications redirect users during error conditions, those redirections were invisible to security tooling.
User training gaps: Users couldn't distinguish between legitimate OAuth consent requests and malicious ones. This isn't entirely a training failure—OAuth consent screens are deliberately designed to look trustworthy.
Relevant Standards
NIST 800-53 Rev 5 IA-2(1) requires multi-factor authentication for network access, but OAuth applications that receive consent can inherit authenticated sessions. Your implementation must enforce Conditional Access policies that evaluate application trust before granting session inheritance.
ISO/IEC 27001:2022 Annex A.9.4.2 addresses secure log-on procedures. This includes controlling which applications can authenticate users. You need documented procedures for OAuth application registration, including:
- Who can register applications
- What review process applications undergo
- How permissions are scoped and approved
- When applications are re-evaluated
OWASP ASVS v4.0.3 Section 3.1.1 requires that applications verify the authenticity of authentication assertions. When your systems accept OAuth tokens, you must validate the issuing application's trustworthiness, not just the token's cryptographic validity.
SOC 2 Type II CC6.1 (Logical and Physical Access Controls) requires that access is granted based on job responsibilities. OAuth consent that grants broad permissions to unknown applications violates this control. Your access control matrix must include OAuth applications as subjects requiring authorization.
Microsoft's recommendation to "tighten permissions for OAuth applications" maps directly to PCI DSS v4.0.1 Requirement 7.2.2: access privileges are assigned based on job function. Each OAuth application should have documented business justification and minimal necessary permissions.
Action Items for Your Team
Immediate actions (this week):
Audit your OAuth application inventory. In Microsoft Entra ID, review Enterprise Applications and App Registrations. For each application, document: business owner, purpose, permissions granted, and last review date. If you can't answer these questions for an app, revoke its permissions.
Enable admin consent requirements for OAuth applications. Users should not be able to grant permissions to applications without security team approval. This is a configuration change in your identity provider—no development work required.
Implement Conditional Access policies that evaluate application risk signals before allowing authentication. At minimum, block consent to applications from unverified publishers.
This month:
Deploy monitoring for OAuth error flows. Your SIEM should alert on redirect_uri parameters pointing to non-allowlisted domains. This is a detection gap in most security programs.
Review and restrict OAuth redirect URIs to specific allowlisted domains for each registered application. Wildcard redirects are a security anti-pattern that enables these attacks.
Conduct tabletop exercises where your security team walks through OAuth attack scenarios. Most teams can explain phishing but struggle to articulate how OAuth consent abuse works.
This quarter:
Build an OAuth application lifecycle management process. This includes: registration approval, quarterly access reviews, automated permission auditing, and decommissioning procedures. Treat OAuth apps like you treat service accounts—they're non-human identities with significant privileges.
Implement application reputation scoring. Before allowing consent, evaluate: publisher verification status, requested permissions scope, domain age of redirect URIs, and historical usage patterns.
Deploy user-facing indicators of application trust. When users see a consent screen, they should have clear signals about whether your organization has vetted this application. Consider browser extensions or identity provider customizations that add trust badges.
The hard truth: OAuth attacks succeed because security teams focus on protecting the perimeter while attackers exploit trust relationships inside it. Your users will click phishing links. Your job is ensuring that click doesn't grant persistent access to your environment.
Start with the audit. You can't protect OAuth applications you don't know exist.