The Challenge
Security scanning tools often generate excessive noise. Your team is likely familiar with this issue. A typical enterprise application security (AppSec) program runs static application security testing (SAST), dynamic application security testing (DAST), and software composition analysis (SCA) scans that flag numerous potential vulnerabilities. Security engineers spend significant time triaging these findings. Developers receive tickets long after writing the code, losing context and often disputing findings they don't understand. Fix rates hover around 30-40%.
Best Buy encountered this problem. Their security team needed a way to reduce false positives while speeding up actual vulnerability remediation. The traditional approach—scanning in CI/CD, filing tickets, and waiting for developers to fix—wasn't keeping pace with their development speed.
The Environment and Constraints
Best Buy operates in a PCI DSS v4.0.1 environment where Requirement 6.2.4 mandates identifying and addressing security vulnerabilities. They couldn't accept a high false positive rate or slow remediation cycles. Unfixed vulnerabilities posed compliance risks and potential exposure of payment card data.
Their development teams used modern IDEs—Visual Studio Code, IntelliJ, Eclipse—writing code rapidly and shipping frequently. The security team needed a solution that:
- Integrated with existing developer workflows without requiring tool changes
- Reduced alert fatigue by improving the signal-to-noise ratio
- Compressed the time between vulnerability introduction and remediation
- Provided actionable guidance developers could act on immediately
Traditional AppSec tools couldn't meet these needs. Scanning after code commit meant vulnerabilities persisted in the codebase for hours or days. Centralized security dashboards created friction—developers had to leave their IDE, log into another system, and switch contexts to understand findings.
The Approach Taken
Best Buy implemented Checkmarx One Developer Assist, an AI-powered security tool that runs directly in the IDE. This marked a shift: instead of scanning code post-commit, the tool analyzes code as developers write it.
The implementation focused on three technical capabilities:
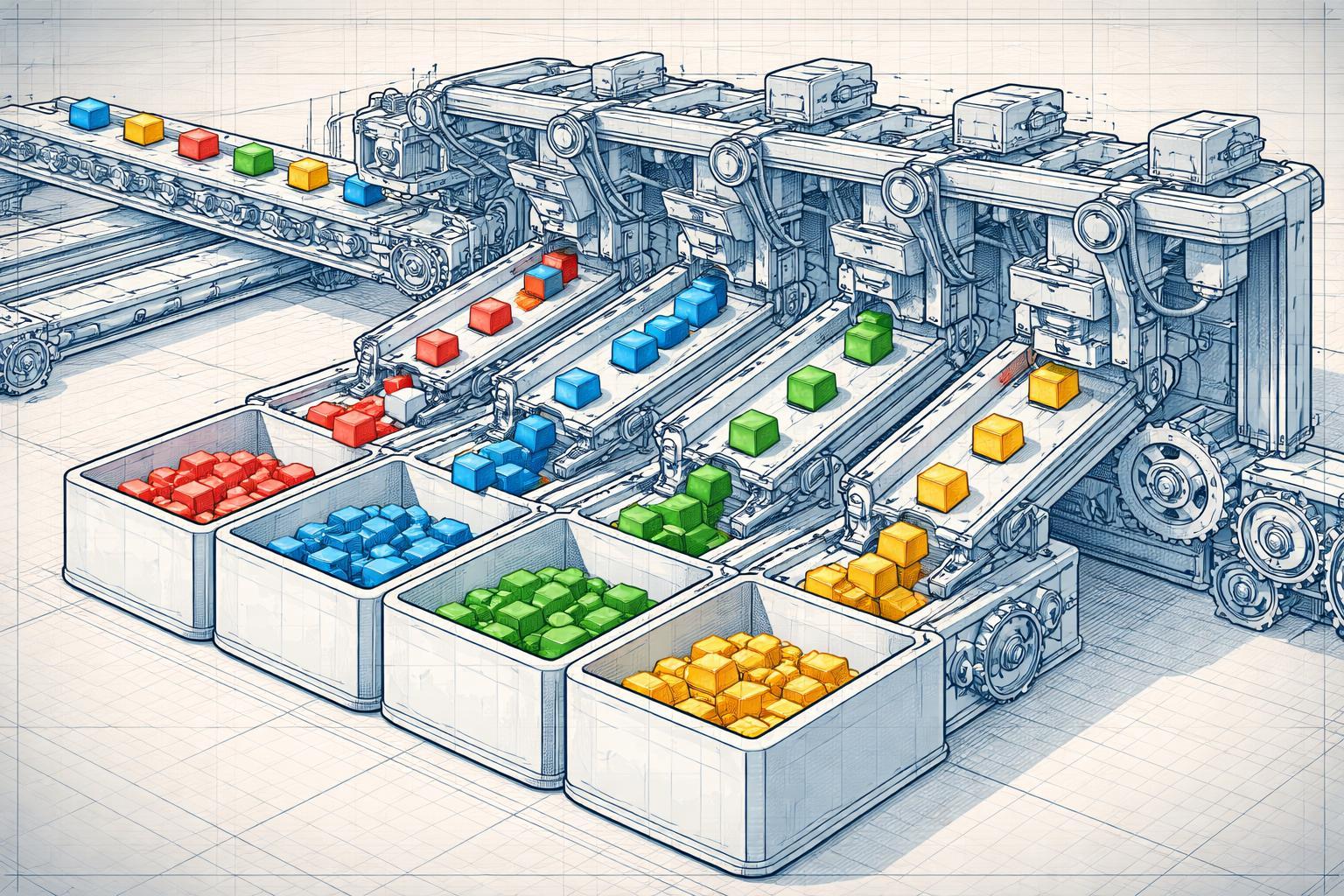
Real-time vulnerability detection: The AI agent continuously scans code in the IDE, flagging security issues before developers commit. This catches SQL injection, XSS, insecure deserialization, and other OWASP Top 10 risks at the point of creation.
Contextual triage: The AI understands code context—data flow, input validation, sanitization controls—to differentiate between exploitable vulnerabilities and false positives. It analyzes whether a potential vulnerability is actually reachable and exploitable given the surrounding code.
Automated remediation guidance: When the tool flags a real issue, it provides specific fix recommendations in the IDE. Developers see exactly which lines need changes and why, often with suggested code snippets.
This approach aligns with Gartner's framework for AI Code Security Assistance, which emphasizes shifting security analysis to the earliest possible point in the development lifecycle.
Results and Metrics
Best Buy reduced false positives by 80%. This is a significant change in their security program's operation.
Consider the impact: If your security tools previously flagged 1,000 findings per month with 600 false positives, your team wasted hundreds of hours on triage. An 80% reduction means only 120 false positives, freeing security engineers to focus on real vulnerabilities and architectural risks.
The time compression was equally significant. Fixing vulnerabilities in the IDE compresses triage and remediation from hours to minutes. A developer sees the issue immediately, understands the context (because they just wrote the code), and fixes it before moving to the next task. No ticket queue. No context switching. No "I don't remember why I wrote it that way" conversations weeks later.
For compliance teams, this changes evidence collection. Instead of showing auditors that you scan monthly and remediate within 90 days, you demonstrate continuous security validation at code creation. This strengthens your control posture for PCI DSS Requirement 6.2.4 and ISO 27001 Annex A.8.8 (management of technical vulnerabilities).
Lessons for Implementation
Based on the technical approach, organizations implementing similar tools should consider:
Start with high-risk repositories: Don't roll out IDE-integrated security tools to every team simultaneously. Begin with applications that process sensitive data or face regulatory requirements. This focuses initial effort where risk reduction matters most.
Measure baseline noise before implementation: Document your current false positive rate and average remediation time. You need these numbers to demonstrate ROI and justify continued investment.
Train developers on the "why": IDE-integrated tools work best when developers understand the security principles behind the findings. A tool that flags SQL injection is more effective when developers understand parameterized queries and why string concatenation creates risk.
Takeaways for Your Team
If you're evaluating AI AppSec tools, focus on three technical criteria:
Context awareness: The tool must understand code flow, not just pattern-match. Ask vendors: "How does your tool differentiate between a SQL injection vulnerability in user-facing code versus a similar pattern in a test fixture?" Tools that can't answer this will generate noise.
IDE integration depth: "Works in the IDE" isn't enough. The tool should provide inline annotations, fix suggestions, and remediation guidance without forcing developers to open external dashboards. Test this during proof-of-concept.
Measurable noise reduction: Demand metrics. If a vendor claims their tool reduces false positives but can't show you data from existing customers, walk away. Best Buy's 80% reduction is the benchmark.
For compliance managers, AI AppSec tools strengthen your control environment in three ways:
- Continuous validation: You're not relying on periodic scans that miss vulnerabilities introduced between scan cycles.
- Faster remediation: Compressing fix time from hours to minutes reduces your window of exposure.
- Developer adoption: Tools that work within existing workflows see higher adoption than those requiring process changes.
The shift from post-commit scanning to real-time IDE analysis isn't just about efficiency—it's about building security into the development process at the point where it's cheapest and most effective to address. Your developers write the code. Give them the tools to write it securely the first time.
AI Code Security Assistance