What happened
TeamPCP, a threat actor group, published two malicious versions of the legitimate Telnyx package on the Python Package Index (PyPI). Versions 4.87.1 and 4.87.2 contained malware hidden inside a WAV audio file using steganographic techniques. The compromised package targeted SSH keys, cloud credentials, and authentication tokens from systems that installed these versions. Given that the legitimate Telnyx package receives over 740,000 downloads per month, the attack surface was substantial.
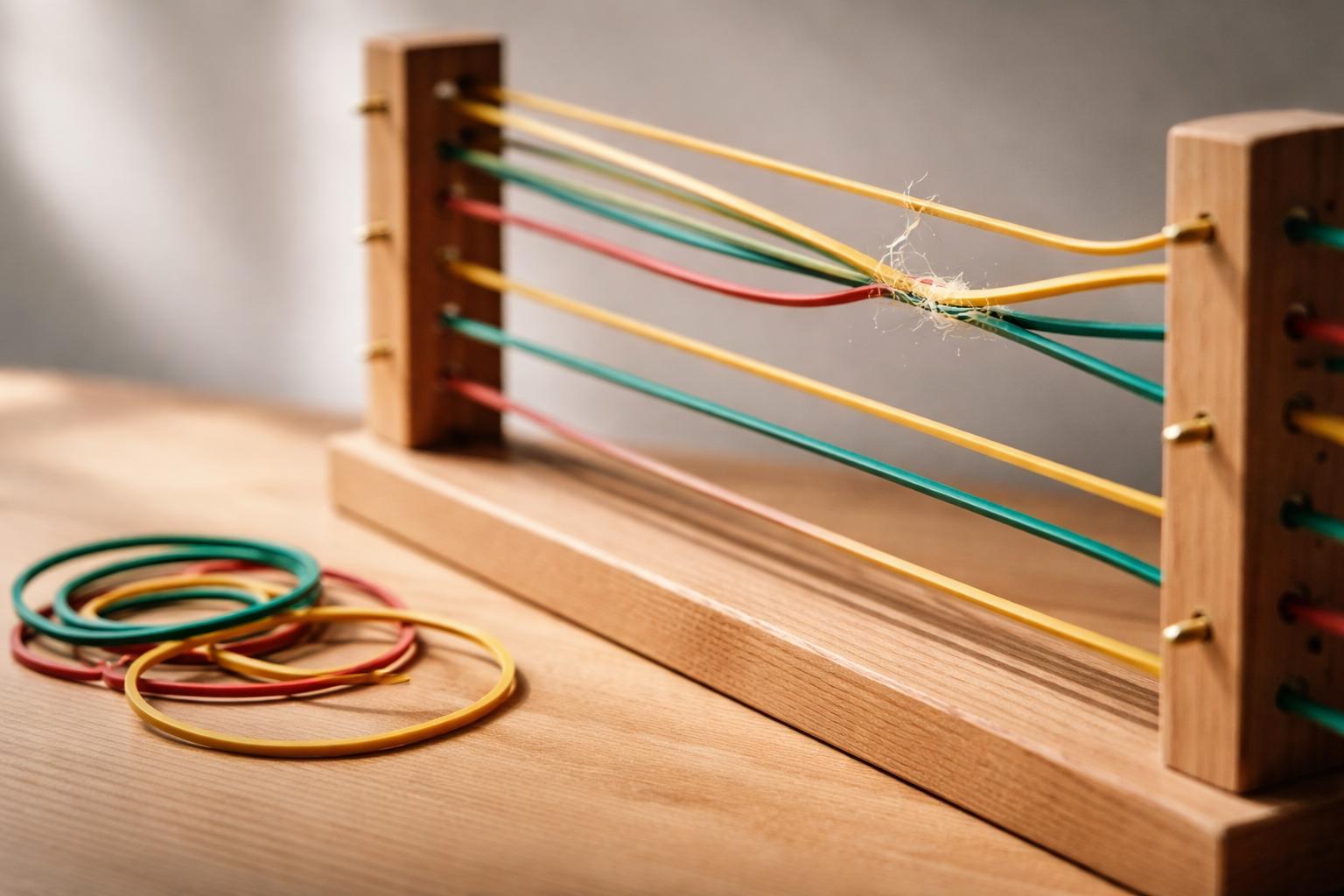
The attackers embedded their payload inside an audio file that appeared benign to standard scanning tools. When the package executed, it extracted and ran the concealed malware, exfiltrating credentials to attacker-controlled infrastructure.
Timeline
The public timeline remains limited, but the attack pattern follows a familiar supply-chain compromise sequence:
- Attackers gained publishing access to the Telnyx package namespace on PyPI.
- Published malicious versions 4.87.1 and 4.87.2 with steganographic payloads.
- Legitimate users installed the compromised versions through normal package management workflows.
- Malware executed during package installation or import, extracting credentials.
- PyPI and the legitimate package maintainers identified and removed the malicious versions.
The gap between publication and detection represents the window where your systems were vulnerable. If you pulled these versions during that window, the malware ran before anyone knew to look for it.
Which controls failed or were missing
Package integrity verification: The attack succeeded because PyPI's namespace allowed the attackers to publish under the legitimate package name. This points to a credential compromise—either the maintainer's PyPI account was breached, or API tokens were stolen and reused.
Dependency scanning limitations: Standard security scanners look for known malicious patterns in code. Steganography defeats signature-based detection because the malicious payload doesn't exist as readable code until runtime. Your dependency scanner saw a WAV file and moved on.
Runtime monitoring gaps: The malware executed during package installation or first import. Without runtime monitoring in your build and deployment pipelines, you wouldn't see the credential exfiltration happening.
Credential exposure: The attack targeted SSH keys, cloud tokens, and authentication credentials. These artifacts were accessible to the malicious package, which means they existed in the environment where packages were being installed—likely developer workstations or CI/CD runners.
What the relevant standards require
NIST 800-53 Rev 5 SA-10 (Developer Configuration Management) requires organizations to track and control changes to software components. This includes verifying the integrity of acquired software products. Your dependency management process needs to detect when a package version changes unexpectedly or when new versions appear without corresponding release notes.
NIST 800-53 Rev 5 SR-4 (Provenance) addresses supply chain risk by requiring documentation and verification of the provenance of system components. For open-source dependencies, this means tracking where packages come from, who publishes them, and whether the publisher identity has been verified.
ISO/IEC 27001:2022 Annex A.8.30 (Outsourced Development) requires security controls for externally developed software. While open-source isn't traditional outsourcing, the principle applies: you're running code written and published by external parties. You need controls to verify that code before it executes in your environment.
PCI DSS Requirement 6.3.2 mandates that custom software is developed securely according to industry standards. The requirement extends to third-party components: you must identify and manage security vulnerabilities in all software components, including dependencies.
SOC 2 Type II CC6.8 requires monitoring of system components for security vulnerabilities. This includes third-party software components. Your evidence needs to show that you're tracking dependencies, monitoring for known vulnerabilities, and responding to supply-chain compromises.
None of these standards explicitly mention steganography, but they all require you to verify the integrity of software components before they run in your environment. The Telnyx compromise demonstrates what happens when verification stops at "Does this package name match what I requested?"
Lessons and action items for your team
Implement package hash verification: Pin your dependencies to specific versions with cryptographic hashes. In Python, use pip-tools to generate requirements.txt files with hashes, or use Poetry with lock files. When a package version changes, your build fails rather than silently pulling compromised code.
Monitor for unexpected version publications: Set up alerts for new versions of your critical dependencies. If a package that typically releases quarterly suddenly publishes three versions in one day, investigate before upgrading. Tools like Dependabot and Renovate can be configured to notify rather than auto-merge.
Isolate credential access: Your build environment shouldn't have access to production credentials. Use separate service accounts for CI/CD with minimal permissions. If a malicious package runs during your build, it should find nothing worth stealing. SSH keys and cloud tokens should never exist in environments where you're installing untrusted code.
Add runtime monitoring to build pipelines: Deploy tools that monitor network activity during builds. A package installation that attempts to connect to external servers should trigger alerts. Solutions like Falco or custom network policies can detect exfiltration attempts even when the malware uses steganography.
Audit your dependency tree regularly: Run pip list or equivalent and review what's actually installed. Compare against your declared dependencies. Malicious packages often masquerade as typosquats or compromised legitimate packages—you need to know what's running in your environment.
Implement software bill of materials (SBOM): Generate and maintain SBOMs for your applications. When a supply-chain compromise is disclosed, you can immediately identify whether you're affected rather than searching through git history and deployment logs.
Verify package publisher identity: PyPI now supports trusted publishing using OpenID Connect. For critical dependencies, verify that the package uses trusted publishing and that the publisher identity makes sense. A package maintained by a major company shouldn't suddenly be published by an unknown account.
The steganographic technique used here is novel, but the underlying failure is not: a trusted package namespace was compromised, and systems that installed the package had access to valuable credentials. Fix the credential exposure and you limit the damage even when the next sophisticated technique bypasses your scanning tools.