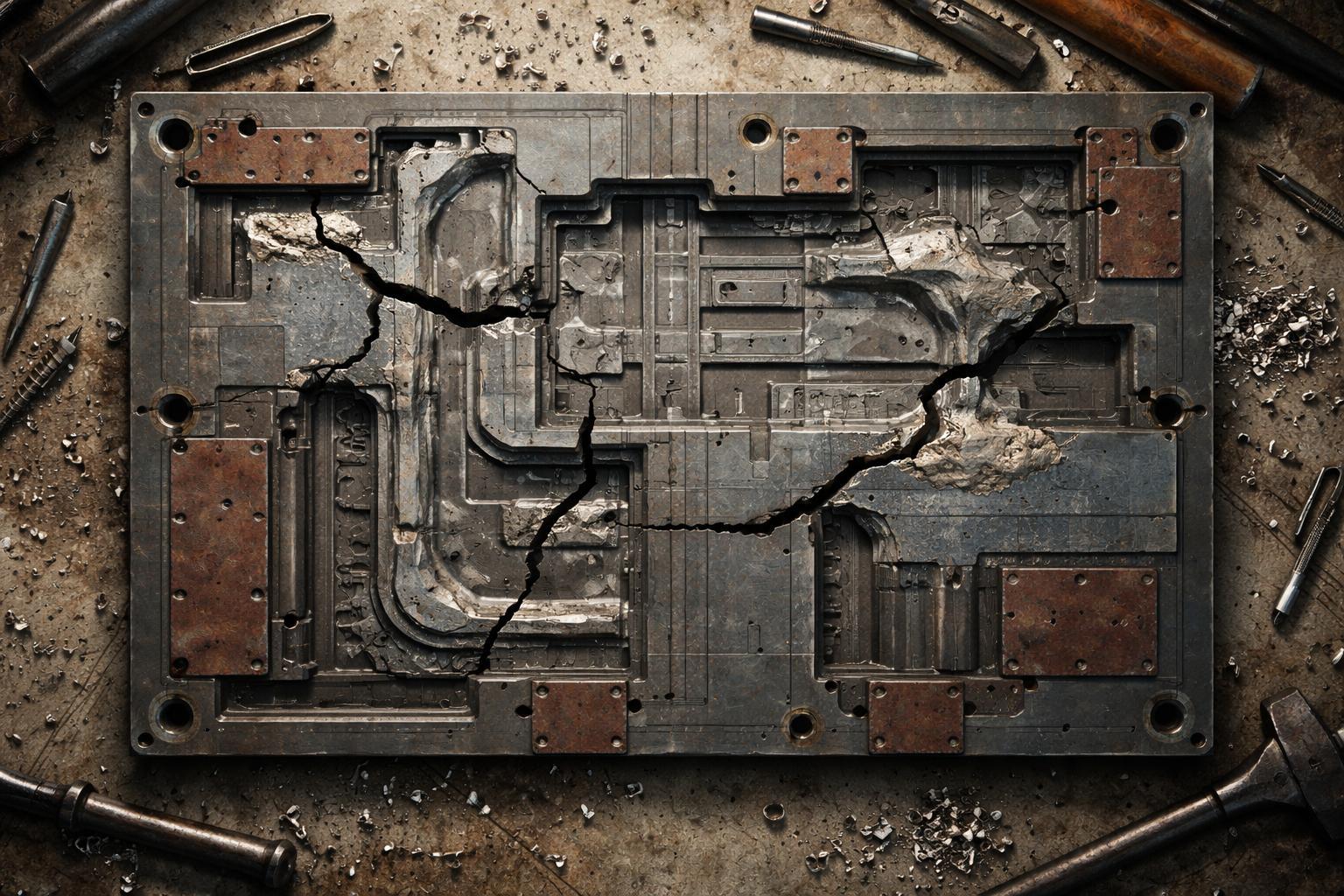
Incident
IncidentA Threat Intelligence Program That Couldn't Detect Threats
Your security team invested in threat intelligence feeds, built a threat modeling framework, and ran quarterly vulnerability assessments. Yet, an adversary exploited a gap you d documented but never v